As businesses accelerate their adoption of cloud technologies, cloud security has emerged as a cornerstone of modern IT strategy. The cloud’s scalability, flexibility, and innovation opportunities empower enterprises to grow and compete globally. However, this freedom comes with inherent risks—creating an expansive attack surface that demands robust security measures.
This article delves into the importance of cloud security, the risks of cloud security breaches, and how advanced solutions can provide end-to end protection.
What is Cloud Security?
Cloud security refers to a set of technologies, policies, and practices designed to safeguard cloud environments from unauthorized access, data breaches, and other threats. It enables organizations to reap the benefits of cloud computing—scalability, innovation, and efficiency—without compromising sensitive data or operational integrity.
As a vital component of modern IT strategies, implementing effective cloud security is complex due to shared responsibilities between service providers and customers, ensuring compliance across jurisdictions, and maintaining consistent policy enforcement in multi-cloud or hybrid environments.
What is Cloud Security Breach?

Cloud security breaches highlight the importance of proactive security measures, thorough audits, and adherence to the best practices when using cloud services. It occurs when unauthorized individuals gain access to sensitive data, applications, or systems hosted in the cloud.
These breaches can result in data theft, service interruptions, financial loss, or reputational damage. Organizations should evaluate their cloud providers’ security capabilities and ensure compliance with relevant regulations to reduce risks. Here are key aspects of cloud security breaches.
- Causes: breaches can arise from misconfigurations (e.g., improperly secured cloud storage), weak access controls, exploitation of software vulnerabilities, or insider threats.
- Types of data at risk: such as sensitive data, including personal, financial, or proprietary business information, can be compromised.
- Attack vectors, such as phishing, exploitation of misconfigurations, and advanced persistent threats (APTs).
- Preventive Measure including encryption, implementing Identity and Access Management (IAM), continuous monitoring, and zero trust architecture.
How Vulnerable is Your Cloud Ecosystem?
The dynamic nature of cloud ecosystem makes it inherently difficult to secure. The constantly evolving attack surface, combined with a lack of visibility and the rapid pace of application development, poses significant challenges to businesses. As organizations adopt multi-cloud and hybrid cloud environments, as well as containerized and serverless architectures, the complexity and risks grow exponentially. CrowdStrike compiles three key vulnerable that can threaten your cloud ecosystem.
1. Complexity in Multi-Cloud and Hybrid Environments Reduces Visibility
Managing multiple cloud providers and hybrid infrastructures creates significant challenges in maintaining a unified security posture. The issues including increased attack surface, reduced visibility as a cause of lack of centralized monitoring across different environments, and configuration errors can cause data breaches.
2. Cloud Applications and APIs as a Growing Attack Surface
New risks through rapid iterations and deployment in a modern application development including CI/CD pipelines introduce hundreds of code changes daily that can be exploited to insert malicious code or backdoors into cloud environments, APIs as attack vectors are increasingly targeted by attackers, and vulnerabilities within third-party libraries or tools can propagate into your applications, leading to wider exposure across your ecosystem.
3. Cloud Data Exposure Creates Business Risks
Sensitive data exposed in cloud environments introduce severe potential risks, such as unintentional exposure due to misconfiguration in storage or databases, insider threats, and compliance violations that will affect to business reputation.
Top Cloud Security Breach in 2024
Based on current cloud security trends, here are the top five cloud security breaches of 2024:
- Data Exposure via Misconfigurations – Misconfigured cloud services continue to be a top cause of security breaches, especially in public clouds, leading to unauthorized data access.
- Ransomware Attacks – Ransomware targeting cloud environments is increasing, exploiting vulnerabilities in cloud infrastructure.
- Cloud Storage Compromise – Insecure cloud storage solutions are increasingly targeted for data breaches, impacting organizations storing sensitive data.
- Supply Chain Attacks – Cybercriminals targeting cloud-based third-party services for broader network infiltration are growing.
- API Exploits – Exploiting vulnerabilities in cloud APIs remains a significant threat, enabling attackers to gain unauthorized access and manipulate systems.
Read More: 6 Reasons Why Your Business Needs to Focus on Cloud Security
CloudStrike: Stop Breaches from Code to Cloud Security
CrowdStrike Code to Cloud Security is a comprehensive protection throughout the entire lifecycle of an application, from development to deployment and execution in the cloud. This end-to-end approach is essential as cloud environments grow increasingly complex and development practices become more agile.
With the surge in cloud adoption and more sophisticated cyber-attacks, the need for robust security measures has never been greater. In the past year, CrowdStrike reported a significant 75% increase in cloud-based exploitation attempts. The average time attackers take to move from an initial breach to system control—referred to as breakout time—is just 62 minutes. This highlights the urgent need for preemptive security measures that can swiftly detect and block threats before they compromise critical systems.
CrowdStrike’s Falcon Cloud Security provides unified protection that operates across the entire cloud security lifecycle. This includes agent-based and agentless security options to safeguard applications at every stage of their development and deployment.
With unique code to cloud security solution, CrowdStrike integrates deeply into the DevOps and CI/CD pipelines. This approach is built into the development workflow to give flexible deployment option to various cloud architectures and operational preferences.
Benefit and USP
 Falcon Cloud Security Platform, Source CrowdStrike
Falcon Cloud Security Platform, Source CrowdStrike
As a cloud security solution, CrowdStrike offers 89 percent faster cloud detection and response, with 100x fewer false positives. Named as Leader by The Forrester Wave: Cloud Workload Security, Q1 2024, CrowdStrike improve 71 percent in policy consistency across cloud environments.
Falcon Cloud Security is the only solution combining both agent-based and agentless protection from code to cloud. Here are six benefits of CrowdStrike solution to secure your cloud environment:
- Complete Visibility: Gain comprehensive insight into your entire cloud infrastructure, workloads, and applications.
- Continuous Security: Prevent misconfigurations from the outset to stop breaches at runtime.
- Risk-Based Prioritization: Reduce alert fatigue and false positives by assessing vulnerabilities based on exploitability and potential impact.
- Seamless Workflows: Break down silos and empower teams to address the most critical issues first.
- Superior Threat Intelligence: Stay ahead of adversaries with protection backed by CrowdStrike’s industry-leading threat intelligence covering 230+ adversaries.
- Expertise on Demand: Bridge the cybersecurity skills gap with expert services in threat hunting, incident response, and managed detection and response (MDR).
Key Features
CrowdStrike is built with the most advanced features to stop attacks, while providing multiple layers of cloud security protection.
Comprehensive Cloud Security Platform
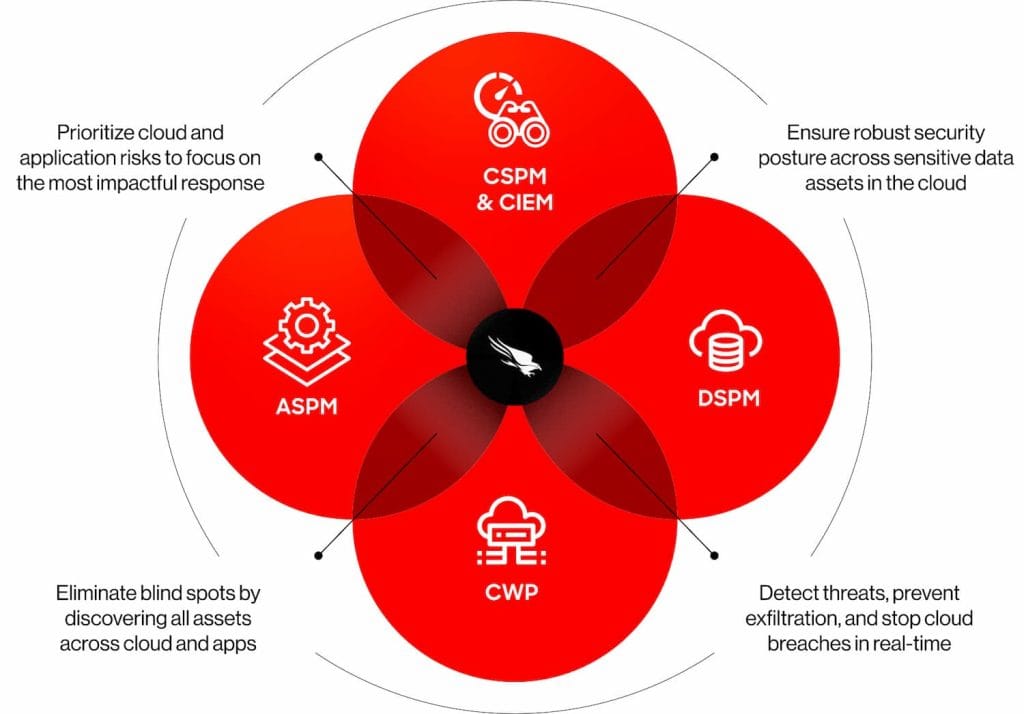
CrowdStrike Falcon Cloud Security delivers a unified approach to cloud security by integrating multiple capabilities, including:
- Cloud Workload Protection (CWP)
- Cloud Security Posture Management (CSPM)
- Cloud Infrastructure Entitlement Management (CIEM)
- Cloud Detection and Response (CDR)
- Application Security Posture Management (ASPM)
These functions are seamlessly consolidated into a single console alongside other CrowdStrike modules, providing unparalleled visibility, advanced threat detection, and real-time response across the entire cloud-native environment.
Understanding Business Impact of Threats
CrowdStrike maps and identifies all components of cloud applications, including microservices, databases, APIs, and dependencies, offering rich context for each. This allows organizations to evaluate the criticality of vulnerabilities and threats in relation to their business impact, ensuring precise prioritization of risks across every attack surface.
Intelligent Risk Prioritization
By utilizing AI and machine learning, CrowdStrike automates the process of risk scoring to streamline threat analysis. It combines CVSS scores with crucial business factors—like the presence of sensitive data and evidence of active exploitation—empowering analysts to focus on the most critical alerts and respond effectively.
Proactive Threat Prevention
With its advanced runtime protection, CrowdStrike stops cloud-based threats in real-time. Built on the same powerful unified agent that powers its industry-leading Endpoint Detection and Response (EDR) and Identity Protection, the Falcon platform provides comprehensive visibility, detection, and response across all cloud-native workloads, containers, and Kubernetes environments, ensuring robust defense against breaches.
Virtus as an Authorized Distributor of CrowdStrike Cloud Security
Virtus Technology Indonesia (Virtus) as an authorized partner of CrowdStrike helps you deliver comprehensive cloud security solutions to protect your business. As part of the CTI Group, Virtus is supported by a competent and certified IT team to help you through the CrowedStrike implementation process from the consulting stage to after sales support.
Interested in implementing the CrowdStrike solution? Click the following link for further consultation.
Author: Ervina Anggraini – Content Writer CTI Group



























