In an increasingly complex digital era, the implementation of NIST Cyber Security Frameworks (NIST CSF) has become critical for businesses to protect their sensitive assets and data. NIST CSF offers a structured and flexible approach to managing cybersecurity risks, which can be tailored to the specific needs of each organization or company.
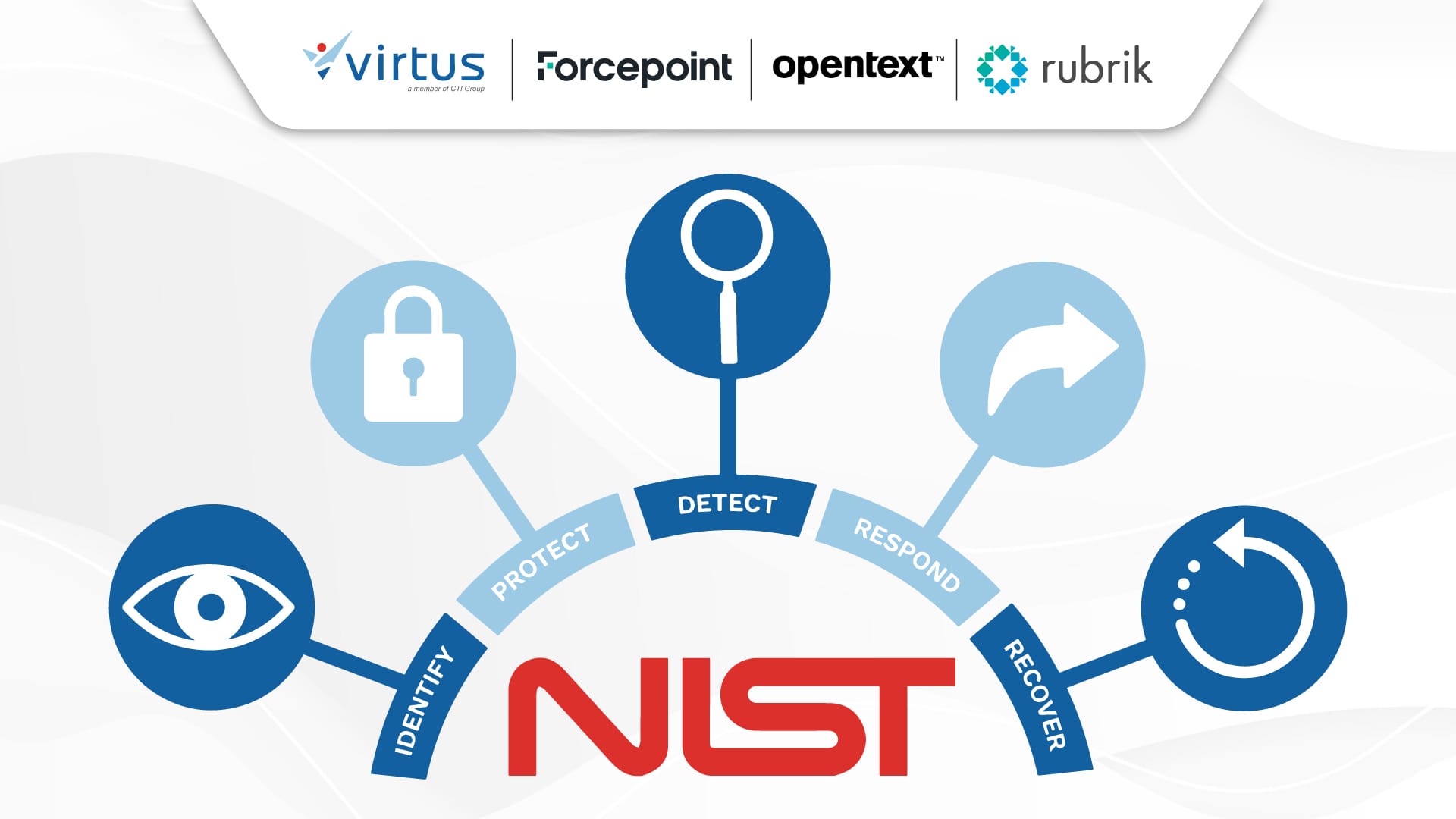
By following this framework, companies can not only improve their resilience to cyberattacks but also build stronger trust with partners and customers. The implementation of NIST CSF involves five functions: Protection Identification, Detection, Response, and Recovery. Each of these functions provides practical guidance to assist companies in identifying critical assets, implementing appropriate protection measures, and responding to and recovering from security incidents. This article will discuss five effective steps that can help businesses implement NIST CSF to avoid cyber threats.
What is the NIST Cybersecurity Framework and Its Importance for Business
The NIST Cybersecurity Framework is a set of guidelines designed to help organizations manage and mitigate cybersecurity risks. The guide, developed by the National Institute of Standards and Technology (NIST), is a framework that provides a common language and systematic methodology for managing cybersecurity risks. That way, organizations can better understand, communicate, and manage cybersecurity efforts.
The NIST Cybersecurity Framework is not only a checklist, but also a flexible tool for IT teams to tailor each organization’s unique needs, risk profile, and resources. This guideline provides a scalable approach to protecting the digital assets of small to large enterprises entering the digital realm.
Core Structure of NIST Cybersecurity Framework
The NIST Cybersecurity Framework is organized into five core functions that represent cybersecurity activities within an organization. These five functions are no different from the pillars that support your cybersecurity strategy.
1. Identify
The Identify function is to gain a deep understanding of the organization’s context, resources, and risks by involving:
- Asset management: categorize your physical and digital assets.
- Business environment: recognize the role of the organization in supply chains and critical functions.
- Governance: establishes cybersecurity policies and procedures.
- Risk Assessment identifies potential threats and vulnerabilities.
Common challenge: many organizations struggle with a lack of visibility into assets, leading to unmanaged risk.
Example implementation: regular audits to maintain an up-to-date inventory of all hardware, software, and data assets to assess criticality and vulnerabilities.
2. Protect
The function of Protect is to outline the appropriate protection to ensure the quality of service. Here are the four main functions of Protect:
- Access control: manage user permissions and access.
- Awareness and training: educate employees on cybersecurity best practices.
- Data security: implement encryption and data loss prevention measures.
- Protective technology: implement firewalls, antivirus software, and intrusion prevention systems.
Common challenges: human error as a significant factor in security breaches due to lack of training.
Example implementation: implement Multi-Factor Authentication (MFA) and conduct regular employee training to recognize phishing attempts.
3. Detect
This structure focuses on real-time detection of cybersecurity events involving the following three things:
- Anomalies and events: monitor for suspicious activity.
- Continuous monitoring: monitor networks and systems in real-time.
- Detection process: applies alert thresholds and response protocols.
Common challenge: organizations often face overwhelming security alerts, so that the blink identifies the real threat.
Implementation example: use advanced analytics and machine learning to filter out false positives and highlight critical alerts for swift action.
4. Respond
This function involves the development and implementation of strategies to stem and mitigate the impact of cybersecurity incidents. Respond includes the following stages:
- Response planning: have an incident response plan.
- Communication: coordinating with stakeholders and authorities.
- Analysis: understanding incidents to prevent similar incidents from happening in the future.
- Mitigation: implementing measures to stop the spread and impact of the incident.
Common challenge: delayed response due to lack of a plan that could exacerbate the damage caused by the incident.
Example implementation: form an incident response team and conduct regular training to ensure readiness.
5. Recover
This function supports timely picking to normal operation which includes:
- Recovery planning: developing strategies to restore operations.
- Improvement: learn from incidents to improve resilience.
- Communication: informing stakeholders during recovery actions.
Common challenge: recovery efforts can be hampered by inadequate backups or untested procedures.
Example implementation: regularly back up critical data to a secure location off-site and test the recovery process to make sure it works when needed.
4 Tiers Implementation of NIST Cybersecurity
To ensure businesses have a reliable data protection strategy, the implementation of the NIST cybersecurity framework must go through the following four tiers:
- Tier 1 Partial: at this level, organizations have an unstructured approach to cybersecurity. Security activities are carried out on an ad hoc basis and there is little alignment between cyber risk management and the entire management process of the organization.
- Tier 2 Risko-informed: organizations are beginning to understand the importance of cyber risk management, characterized by the implementation of policies and procedures. However, cross-departmental coordination is still limited and steps taken are still based on specific project needs or risks.
- Tier 3 Repeatable: this stage indicates that the organization has a coordinated and documented cybersecurity approach. Risk management becomes part of business processes with consistent practices across the organization using optimized security technologies and processes.
- Tier 4 Adaptive: organizations proactively identify and respond to cyber threats. At the highest level, organizations improve security strategies based on real-time analysis, threat intelligence, continuous risk evaluation, and cybersecurity integration with organizational culture.
Steps to Implement the NIST Cybersecurity Framework
There are five stages that businesses must go through when implementing the NIST cybersecurity framework, here are the five steps.
1. Conduct an In-Depth Assessment
The first step is to conduct a thorough and in-depth self-assessment of your organization’s cybersecurity posture. The assessment includes an inventory of assets, identification of potential risks and vulnerabilities, and evaluation of existing security controls. This step helps businesses understand the weak points that are prioritized. Make sure to know what your business’s most important assets, biggest threats, and security measures are already in place.
2. Develop a NIST CSF Profile
Every business has unique needs, so a customized NIST CSF profile is needed. Prioritize subcategories based on risk level, industry, and regulatory requirements such as data security to payment transaction protection. Use the risk matrix to assess the likelihood and impact of various threats.
3. Prepare an Implementation Plan
After adjusting the profile as needed, then create a clear and detailed implementation plan. The implementation plan includes specific tasks, deadlines, responsibilities, and resource allocation.
Prepare an implementation plan using a template or checklist. You can also take advantage of project management software to track the progress of your team’s work.
4. Implement Security Controls
This is done to identify the risks and vulnerabilities that have been identified. This stage is the implementation of the “protect” function that implements data encryption and regular security training.
The implementation of security controls can be a combination of technical controls (including firewalls, antivirus software, and MFA), administrative controls (including security policies and procedures), and physical controls (including CCTV to limited access to certain areas).
5. Continuous Monitoring and Improvement
As an ongoing process, cybersecurity needs to be monitored on a regular basis for the effectiveness of security controls. This can be done by assessing risks periodically and adjusting security strategies as needed.
Use tools such as vulnerability scans and SIEM to monitor security controls. Make sure to provide regular training and programs to ensure that all employees understand cybersecurity best practices. Also Read: The Complete Guide for Modern Businesses to Master Cybersecurity with the NIST Cybersecurity Framework
Simplify the Deployment of NIST Cybersecurity Framework with Virtus
Now that you know the five effective stages of implementing the NIST cybersecurity framework to provide a solid security phonation, it’s time to implement the right solution. Virtus Technology Indonesia offers Rubrik, Forcepoint, and Opentext solutions for the implementation of the NIST cybersecurity framework so that you can strengthen your defenses and cybersecurity.
Rubrik
Rubric is a comprehensive, integrated solution with a focus on speed, security, and compliance to help businesses meet NIST CFR data security and compliance standards. The rubric is equipped with three main pillars, namely Data Backup and Recovery, Anomalous Encryption, and Sensitive Data Discovery to provide comprehensive protection for critical data, even during increasingly complex cyber threats. The rubric is equipped with advantages in the form of data backup and recovery, anomalous encryption, and sensitive data discovery.
- Data Backup and Recovery
Fast and reliable data recovery, including when responding to increasingly sophisticated ransomware attacks. The rubric ensures that an organization’s data is always available and protected from attacks or damage with a sophisticated approach, including:
- Immutability: backup data that cannot be changed or deleted, even by users with administrative access for optimal protection against ransomware.
- Global Search: enables a quick and efficient search of lost or damaged data across the environment, saving recovery time.
- Instant Recovery: files or systems are revived in minutes, not days, ensuring business continuity.
- Air Gap: an isolated backup storage option from the production environment for added protection.
Featured Features:
- Synchronous and asynchronous backups for flexibility.
- Global replication to ensure data availability across multiple locations.
- Automated orchestration minimizes human error and increases efficiency.
- Anomalous Encryption
A proactive approach to protecting data by identifying and encrypting suspicious data. The solution uses the latest technology to detect threats early and protect the most important data. Here are the advantages of Rubrik for cracking anomalies:
- Early threat detection: detect suspicious activity or anomalous patterns before potential damage occurs.
- Sensitive data protection: keep valuable data confidential from unauthorized access.
- Ensuring the prevention of the spread of ransomware by not being able to encrypt data that is already protected.
Three outstanding features of Rubrik:
- Machine Learning for accurate analysis of data patterns.
- Automatic encryption to protect sensitive or suspicious data.
- Secure encryption key management to ensure confidentiality.
- Sensitive Data Discovery
Identify sensitive data across environments with high accuracy to understand, track, and protect sensitive data to meet compliance requirements and reduce the risk of data leaks. Here are the advantages of Rubrik:
- Compliance: supports compliance with regulations such as GDPR and HIPAA.
- Risk reduction: minimize the chances of data leaks by detecting and protecting sensitive assets.
- Increased visibility: provides deep insights into the data the organization has.
Rubrik’s top features:
- Automatic data classification based on Machine Learning.
- Data search is flexible with a variety of criteria, including file types, content, and metadata.
- Comprehensive reports to help with data management strategies.
Forcepoint
Forcepoint provides integrated security solutions according to the NIST CFR framework with an adaptive, sophisticated, and user-centric approach. The solution offers a unified platform for managing and enforcing data protection, adaptive security based on user behavior and risk analysis, advanced threat detection with zero-day technology, and maximum protection to minimize disruption to users.
Forcepoint ensures data breach prevention, ensures regulatory compliance, mitigates risk, improves security posture, and increases team productivity. Here are the featured features of Forcepoint:
- Data discovery and classification support the “Identify” process by ensuring sensitive data is identified and categorized.
- Email and web security from external threats, supporting “Protect” and “Detect” steps.
- Cloud application and endpoint security to ensure end-to-end protection across multiple platforms.
- Analyze user behavior by quickly identifying anomalies from internal threats.
- Data protection policies as per business-specific needs to support the implementation of a flexible NIST framework.
- Real-time monitoring and notifications regarding suspicious activity to prevent incidents and provide quick response.
- Respond to incidents efficiently with comprehensive investigation tools to analyze threats and accelerate recovery.
Opentext
Opentext offers world-class data security solutions designed to meet stringent regulatory requirements such as the NIST CFR. With an innovative approach through Voltage products, OpenText provides advanced encryption and data masking to protect sensitive information in a variety of environments.
Opentext is equipped with Format-Preserving Encryption (FPE) technology that allows data to be encrypted without changing the format. With flexibility and easy integration, Opentext offers maximum enterprise-grade data protection. Opentext five features to increase productivity, reduce the risk of data leaks, and ensure regulatory compliance.
- Data Encryption: keeps data stored in various locations secure, including during transmission over the network.
- Static and Dynamic Data Masking: hides sensitive data in use and in storage for long periods of time without affecting business logic.
- Tokenization: replacing sensitive data with unique tokens that have no intrinsic value to prevent misuse.
- Format-Preserving Encryption (FPE): preserves the original format of the data, ensuring compatibility with existing systems and applications.
- Anomaly Detection: monitors for suspicious activity and provides early warnings to prevent security threats.
Implement NIST CSF with Virtus
Virtus Technology Indonesia, part of CTI Group, presents a suite of solutions from Rubrik, Forcepoint, and Opentext to help your business implement NIST CSF quickly and effectively. Virtus is ready to help you implement the NIST Cybersecurity Framework from concept to reality to take business security to the next level.
Virtus as an authorized distributor and partner of Rubrik, Forcepoint, and Opentext ensures an optimal implementation process thanks to the support of a team of professional and certified engineers. Contact the Virtus team today to take proactive steps to protect your business assets.
Author: Ervina Anggraini – Content Writer CTI